Researchers Uncover Spying Tool Used by Governments to Hijack all Types of Smartphones
 |
Researchers Uncover Spying Tool Used by Governments to Hijack all Types of Smartphones |
Researchers from the Citizen Lab at the Munk School of Global Affairs at the University of Toronto and computer security firm Kaspersky Lab
have unearthed a broad network of controversial spyware which is
specially designed to give law enforcement agencies complete access to a
suspect's phone for the purpose of surveillance.
MALWARE FOR DESKTOPS AND ALL MOBILE DEVICES
 |
Researchers Uncover Spying Tool Used by Governments to Hijack all Types of Smartphones |
The team of researchers from
both Citizen Lab and Kaspersky Lab in collaboration has presented their
findings during an event in London. According to the report published,
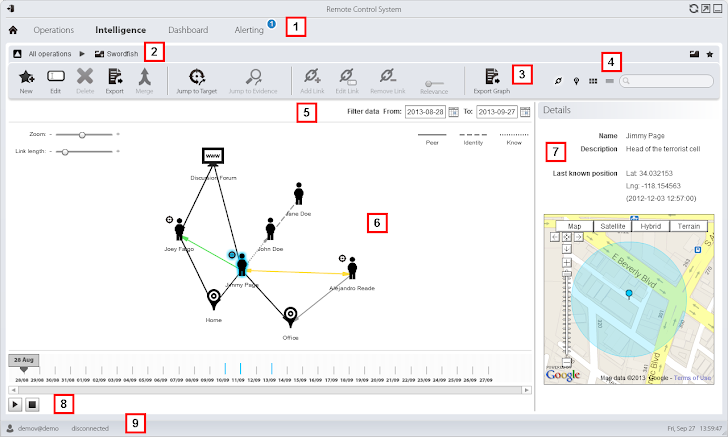
the diameter of the command infrastructure supporting Hacking Team,
which sells the RCS to governments and law enforcement, is very vast
with 326 command-and-control (C&C) servers running in more than 40
countries.
MALWARE DEVELOPERS - ‘HACKING TEAM’
Hacking
Team is a Milan-based IT company with more than 50 employees that has
made a totally different place for itself selling "offensive" intrusion
and surveillance software to governments and law enforcement agencies in "several dozen countries" on "six continents."
“It was a well-known fact for
quite some time that the HackingTeam products included malware for
mobile phones. However, these were rarely seen,” said Kaspersky Lab experts on the blog post. “In
particular, the Android and iOS Trojans have never been identified
before and represented one of the remaining blank spots in the story.”
WORLD WIDE WEB OF COMMAND-N-CONTROL SERVERS
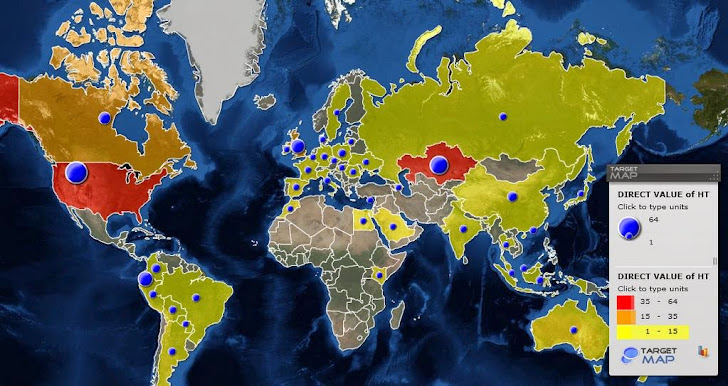 |
Researchers Uncover Spying Tool Used by Governments to Hijack all Types of Smartphones |
"The presence of these servers in a given country doesn't mean to say they are used by that particular country's law enforcement agencies," said Sergey Golovanov, principal security researcher at Kaspersky Lab. "However, it makes sense for the users of RCS to deploy C&Cs in locations they control – where there are minimal risks of cross-border legal issues or server seizures."
ATTACK VECTOR AND MALWARE FEATURES
 |
Researchers Uncover Spying Tool Used by Governments to Hijack all Types of Smartphones |
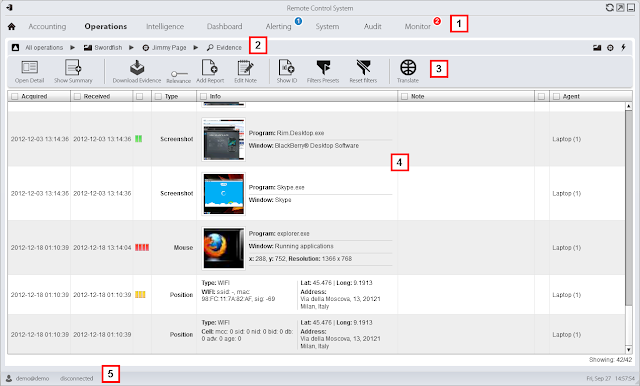
Once installed on Apple iOS and
Android device, the new module enable governments and law enforcement
officers with larger capabilities to monitor victim devices, including
the ability to:
- control phone network
- steal data from their device
- record voice E-mail
- intercept SMS and MMS messages
- obtain call history
- report on their location
- use the device’s microphone in real time
- intercept voice and SMS messages sent via applications such as Skype, WhatsApp, Viber, and much more.
"Secretly activating the microphone and taking regular camera shots provides constant surveillance of the target—which is much more powerful than traditional cloak and dagger operations," Golovanov wrote.
While,
the Android module is protected by an optimizer for Android called
DexGuard that made the it extremely difficult to analyze. However, most
of the iOS capabilities mentioned above are also available for Android,
along with the support for hijacking applications such Facebook, Google
Talk, Tencent of China and many more.
The mobile modules for each are
custom-built for each target, researchers said. From previous
disclosures we have seen that RCS is currently being used to spy on
political dissidents, journalists, human rights advocates, and opposing
political figures.
Source:-thehackernews.com






Post a Comment